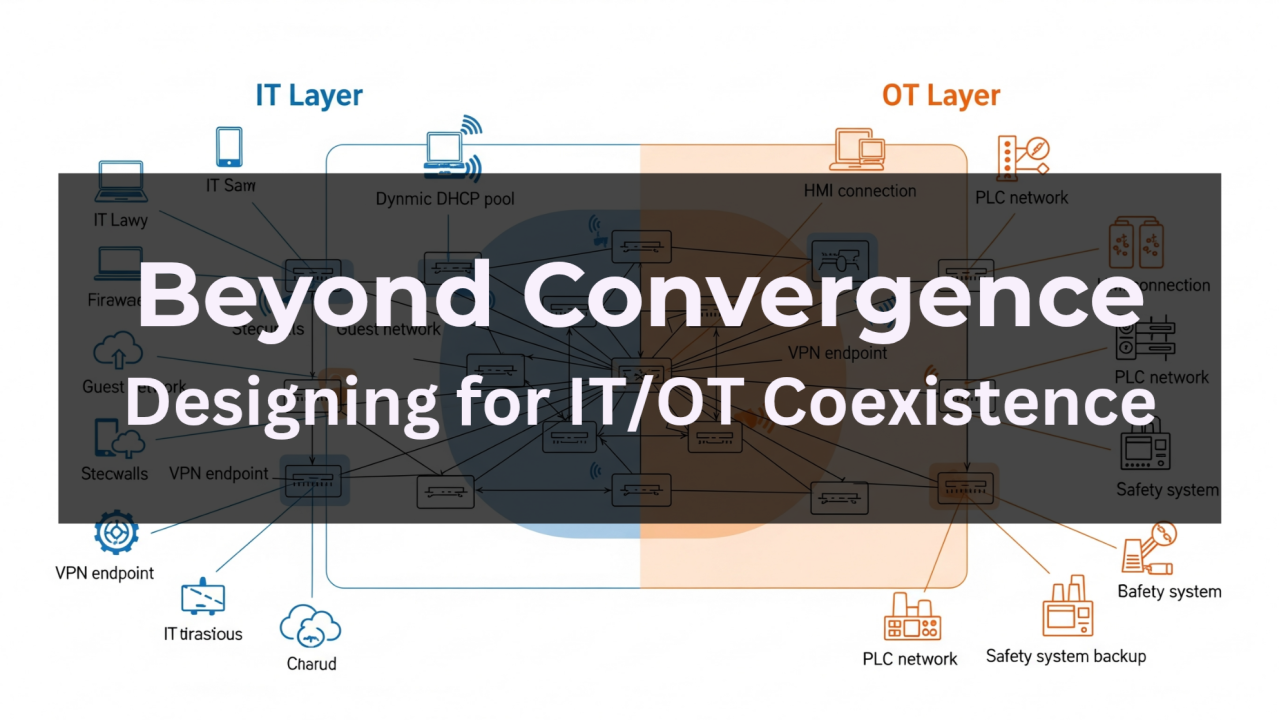
When it comes to network architecture, there's a fundamental divide that often goes unrecognized: the vastly different perspectives of Operational Technology (OT) and Information Technology (IT) teams. Understanding this divide is crucial for anyone designing systems that bridge both worlds.
The IT Perspective: Network as Utility
For IT professionals, the network is essentially a utility... think of it like electricity or water flowing through your building. It's infrastructure that needs to be:
- Flexible and dynamicto serve a constantly changing user base
- Secure to protect valuable corporate assets and sensitive data
- Scalable to accommodate growth and new technologies
- Manageable across diverse devices and applications
IT teams are accustomed to users coming and going, devices being added and removed, and software being updated regularly. Their network designs prioritize adaptability, with robust security policies, user authentication systems, and the ability to segment and control access to different resources.
The OT Perspective: Network as Machine Component
OT professionals see the network completely differently. To them, it's not a utility but an integral component of a production system... as critical as a motor, sensor, or control valve. This perspective drives entirely different priorities:
- Maximum availability (often 99.9%+ uptime requirements)
- Predictable, static configuration that won't interfere with production
- Real-time performancewith minimal latency and jitter
- Proven reliability over cutting-edge features
In manufacturing, power generation, or process control environments, network downtime doesn't just mean inconvenience—it can mean millions of dollars in lost production, safety hazards, or regulatory violations. OT networks are designed to be "set and forget," with minimal changes once commissioned.
Why This Matters
This fundamental difference in perspective creates challenges when OT and IT systems need to converge:
- IT security practices (like automatic updates or network segmentation changes) can disrupt OT operations
- OT's resistance to change can create security vulnerabilities from an IT standpoint
- Network performance requirements may conflict between the two domains
- Troubleshooting approaches and priorities often clash
A Note on "Convergence"
Before we go further, let's address the elephant in the room: the word "convergence." You'll often hear vendors and consultants talk about "OT/IT convergence" as if these two domains are naturally moving toward some unified state.
This is marketing speak, and it's misleading.
The reality is that OT and IT serve fundamentally different purposes with fundamentally different requirements. They're not "converging"—they're being forced to coexist in an increasingly connected world. The goal isn't to make them the same; it's to make them work together while preserving what makes each effective in their respective domains.
True "convergence" would mean compromising the reliability that OT requires or sacrificing the flexibility that IT needs. Neither is acceptable.
Building Bridges (Not Convergence)
Successful convergence requires understanding and respecting both perspectives. Solutions might include:
- Dedicated OT network segments with IT oversight but OT operational control
- Staged security implementations that prioritize availability while gradually improving security posture
- Joint planning processes that bring both teams together early in design phases
- Hybrid architectures that provide IT flexibility where needed while maintaining OT stability where required
The key is recognizing that neither perspective is wrong, they're optimized for different operational realities. The best network architectures acknowledge these differences and design accordingly, rather than trying to force one worldview onto the other.
🌊
What's your experience with OT/IT convergence? Have you seen these different perspectives create challenges, or opportunities, in your organization?